This article is for the people who have just setup Apache web server & wanted to secure it. I am going to tell you the 7 Steps for Securing Apache web server against most common types of attacks today.
I am executing these steps on an Ubuntu 14.04 LTS virtual server.
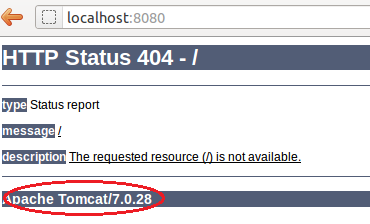
STEP1: Hide Apache Version information from HTTP response
It’s a risky option to show the version of your Apache web server to the visitor. If a hacker comes to know about any vulnerability with your server’s Apache version, chances are that your server can get compromised.
Following method is used to hide Apache version from response headers & signature.
Open /etc/apache2/conf-enabled/security.conf in an editor & modify the following Values to look like below
ServerTokens Prod
ServerSignature Off
STEP2: Disable HTTP methods TRACE & OPTIONS
Disabling OPTIONS & TRACE method is important from security perspective since they are expected to be used for getting Diagnostic information from your server. So For disabling there methods i will have following values in /etc/apache2/conf-enabled/security.conf
TraceEnable Off
RewriteEngine On
RewriteCond %{REQUEST_METHOD} ^OPTIONS
RewriteRule .* – [F]
Make sure that you have enabled mod_rewrite in order for the above rewrite rules to work properly.
STEP3: Restrict uploads directory for only certain file types
Suppose you have a directory “uploads” in the document root and there is a chance that attacker might use different techniques to upload malware code on this directory. To prevent this add the following rules to the virtual host configuration file.
RewriteCond %{REQUEST_URI} ^/uploads [NC]
RewriteCond %{REQUEST_URI} !.(jpe?g|png|gif)$ [NC]
RewriteRule .* - [F,L]
The above code will make sure that only file types allowed to be uploaded are jpg, jpeg, png & gif
STEP4: Mitigate DoS (Slowris) attacks
Since apache is a thread based web server, We need to make sure that it will not get affected by Slowiris DoS attack. Under this vulnerability, the attacker can send slow HTTP requests in huge numbers, thus causing a disruption to your Web server and apache may become unresponsive.
Following fix can be applied to Apache to avoid this attack. Make sure that you have mod_reqtimeout module installed an enabled in Apache.
<IfModule mod_reqtimeout.c>
RequestReadTimeout header=20-40,MinRate=500 body=20,MinRate=500
</IfModule>
STEP5: Protecting against SQL injection attacks
SQL Injection has become a common threat to any website running a MySQL backed a web application. Preventing this is an important step in security. With the power of mod_rewrite & mod_security most of the SQL injection attacks can be prevented.
You can install mod_security & include all CORE rules provided by OWASP
Following are some handy rules using which you can avoid SQL injection attacks. You can place them either in virtual host file or .htaccess
RewriteCond %{QUERY_STRING} [a-zA-Z0-9_]=http:// [OR]
RewriteCond %{QUERY_STRING} [a-zA-Z0-9_]=(..//?)+ [OR]
RewriteCond %{QUERY_STRING} [a-zA-Z0-9_]=/([a-z0-9_.]//?)+ [NC,OR]
RewriteCond %{QUERY_STRING} =PHP[0-9a-f]{8}-[0-9a-f]{4}-[0-9a-f]{4}-[0-9a-f]{4}-[0-9a-f]{12} [NC,OR]
RewriteCond %{QUERY_STRING} (../|..) [OR]
RewriteCond %{QUERY_STRING} ftp: [NC,OR]
RewriteCond %{QUERY_STRING} http: [NC,OR]
RewriteCond %{QUERY_STRING} https: [NC,OR]
RewriteCond %{QUERY_STRING} =|w| [NC,OR]
RewriteCond %{QUERY_STRING} ^(.*)/self/(.*)$ [NC,OR]
RewriteCond %{QUERY_STRING} ^(.*)cPath=http://(.*)$ [NC,OR]
RewriteCond %{QUERY_STRING} (<|%3C).*script.*(>|%3E) [NC,OR]
RewriteCond %{QUERY_STRING} (<|%3C)([^s]*s)+cript.*(>|%3E) [NC,OR]
RewriteCond %{QUERY_STRING} (<|%3C).*iframe.*(>|%3E) [NC,OR]
RewriteCond %{QUERY_STRING} (<|%3C)([^i]*i)+frame.*(>|%3E) [NC,OR]
RewriteCond %{QUERY_STRING} base64_encode.*(.*) [NC,OR]
RewriteCond %{QUERY_STRING} base64_(en|de)code[^(]*([^)]*) [NC,OR]
RewriteCond %{QUERY_STRING} GLOBALS(=|[|%[0-9A-Z]{0,2}) [OR]
RewriteCond %{QUERY_STRING} _REQUEST(=|[|%[0-9A-Z]{0,2}) [OR]
RewriteCond %{QUERY_STRING} ^.*([|]|(|)|<|>).* [NC,OR]
RewriteCond %{QUERY_STRING} (NULL|OUTFILE|LOAD_FILE) [OR]
RewriteCond %{QUERY_STRING} (./|../|.../)+(motd|etc|bin) [NC,OR]
RewriteCond %{QUERY_STRING} (localhost|loopback|127.0.0.1) [NC,OR]
RewriteCond %{QUERY_STRING} (<|>|'|%0A|%0D|%27|%3C|%3E|%00) [NC,OR]
RewriteCond %{QUERY_STRING} concat[^(]*( [NC,OR]
RewriteCond %{QUERY_STRING} union([^s]*s)+elect [NC,OR]
RewriteCond %{QUERY_STRING} union([^a]*a)+ll([^s]*s)+elect [NC,OR]
RewriteCond %{QUERY_STRING} (;|<|>|'|"|)|%0A|%0D|%22|%27|%3C|%3E|%00).*(/*|union|select|insert|drop|delete|update|cast|create|char|convert|alter|declare|order|script|set|md5|benchmark|encode) [NC,OR]
RewriteCond %{QUERY_STRING} (sp_executesql) [NC]
RewriteRule ^(.*)$ - [F,L]
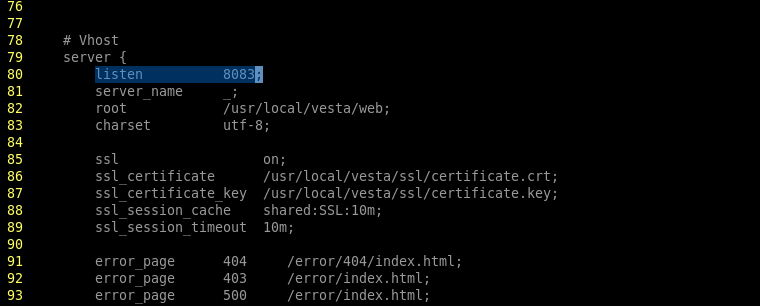
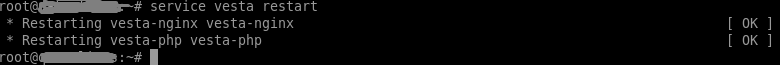
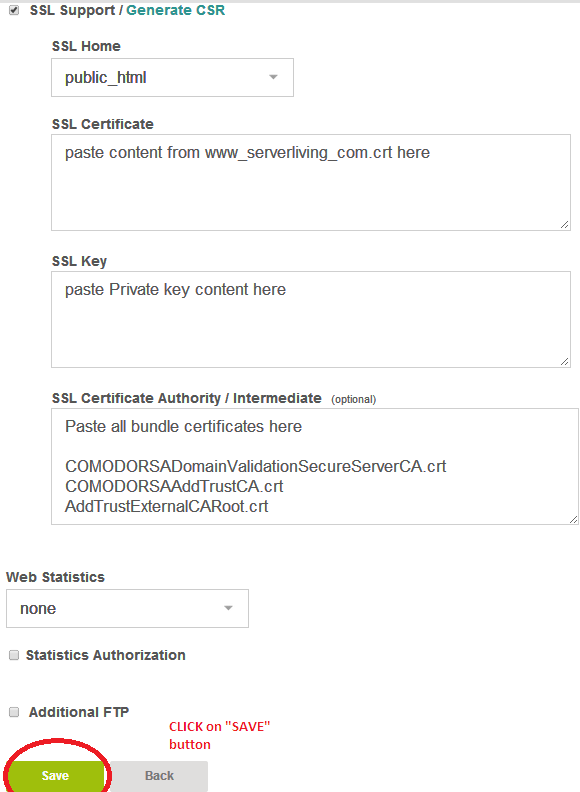
STEP6: Have your website only talk on HTTPS
This step is very important if you are running a transaction based website like Ecommerce, Payment etc. In future google will be ranking the sites up which are serving content over HTTPS.
Following is the configuration which you can use while setting up SSL certificate for your site.
Following rule enforces all requests to be served on HTTPS. Please it in .htaccess file.
Rewritengine On
RewriteCond %{SERVER_PORT} 80
RewriteRule ^(.*)$ https://%{HTTP_HOST}/$1 [R=301,L]
Place the following rules in apache’s virtual host file.
SSLCompression off
SSLProtocol All -SSLv2 -SSLv3 -TLSv1
SSLHonorCipherOrder On
SSLCipherSuite ECDHE-RSA-AES128-GCM-SHA384:ECDHE-RSA-AES128-GCM-SHA128:DHE-RSA-AES128-GCM-SHA384:DHE-RSA-AES128-GCM-SHA128:ECDHE-RSA-AES128-SHA384:ECDHE-RSA-AES128-SHA128:ECDHE-RSA-AES128-SHA:ECDHE-RSA-AES128-SHA:DHE-RSA-AES128-SHA128:DHE-RSA-AES128-SHA128:DHE-RSA-AES128-SHA:DHE-RSA-AES128-SHA:ECDHE-RSA-DES-CBC3-SHA:EDH-RSA-DES-CBC3-SHA:AES128-GCM-SHA384:AES128-GCM-SHA128:AES128-SHA128:AES128-SHA128:AES128-SHA:AES128-SHA:DES-CBC3-SHA:HIGH:!aNULL:!eNULL:!EXPORT:!DES:!MD5:!PSK:!RC4
Header always set Strict-Transport-Security "max-age=63072000; includeSubDomains"
STEP7: Protect your application against DDoS & brute force attacks.
DDoS attacks are severe headache & they can cause a huge downtime on your websites. DDoS attack is done by sending continuous heavy number of requests to your web server so that your Apache is kept busy and hence it will because unresponsive.
There are various firewalls & solutions available for securing apache against DDoS, I would recommend using either Cloudflare CDN or fail2ban firewall.
fail2ban runs on the same machine where apache is running and it will examine requests from specific IP & drops their connections once the threshold is reached. This threshold value can be configured.
To use CloudFlare CDN, you are required to map your website to name servers provided by cloudflare.
Any Thoughts?